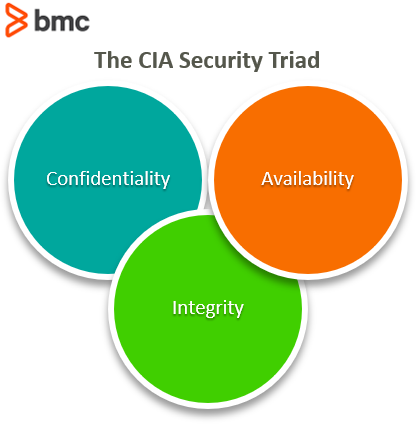
What Is the CIA Security Triad? Confidentiality, Integrity, Availability Explained – BMC Software | Blogs

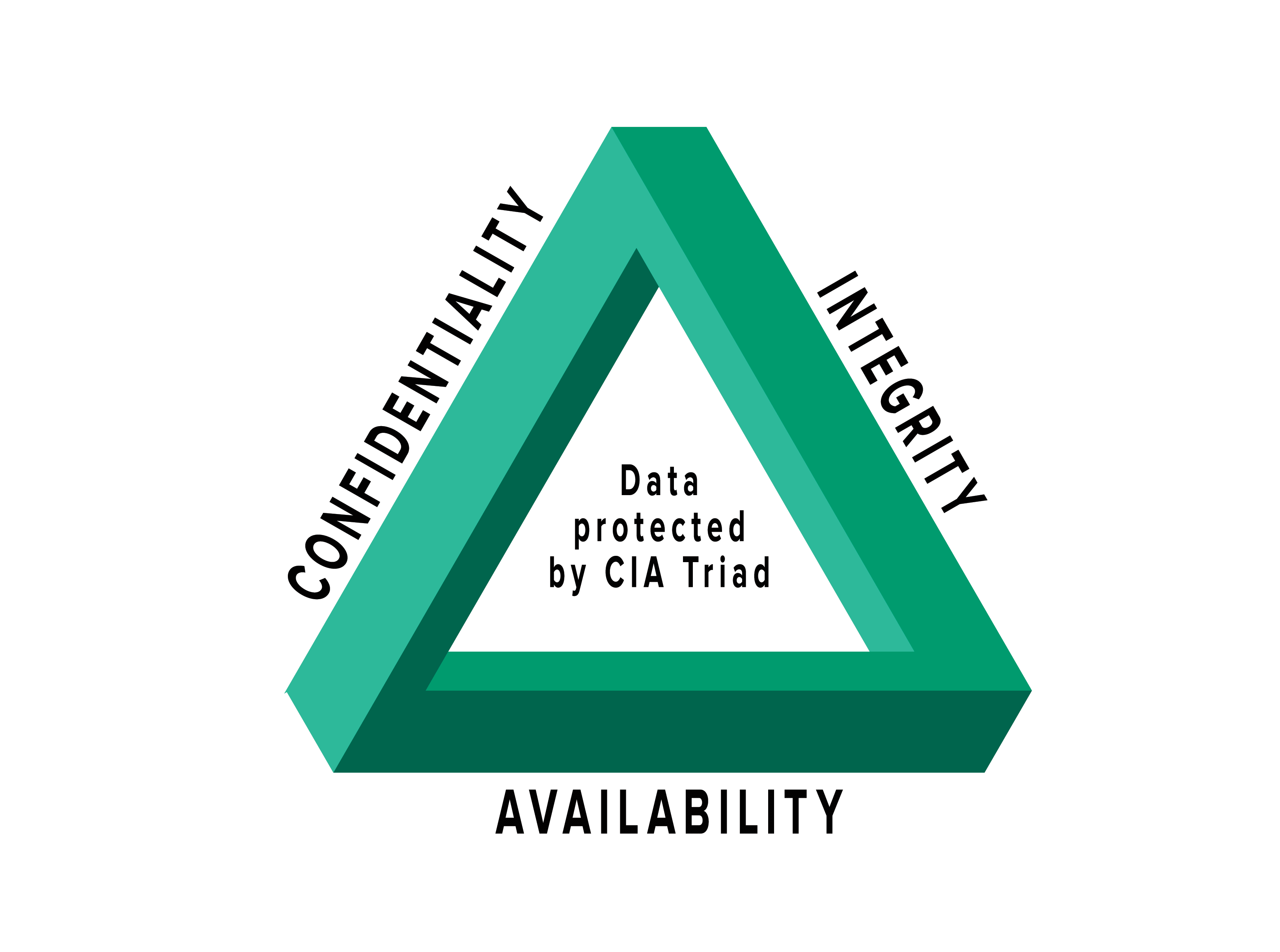
Confidentiality, Integrity, Availability (CIA Triad) — The Backbone of Cybersecurity | by Ensar Seker | DataDrivenInvestor

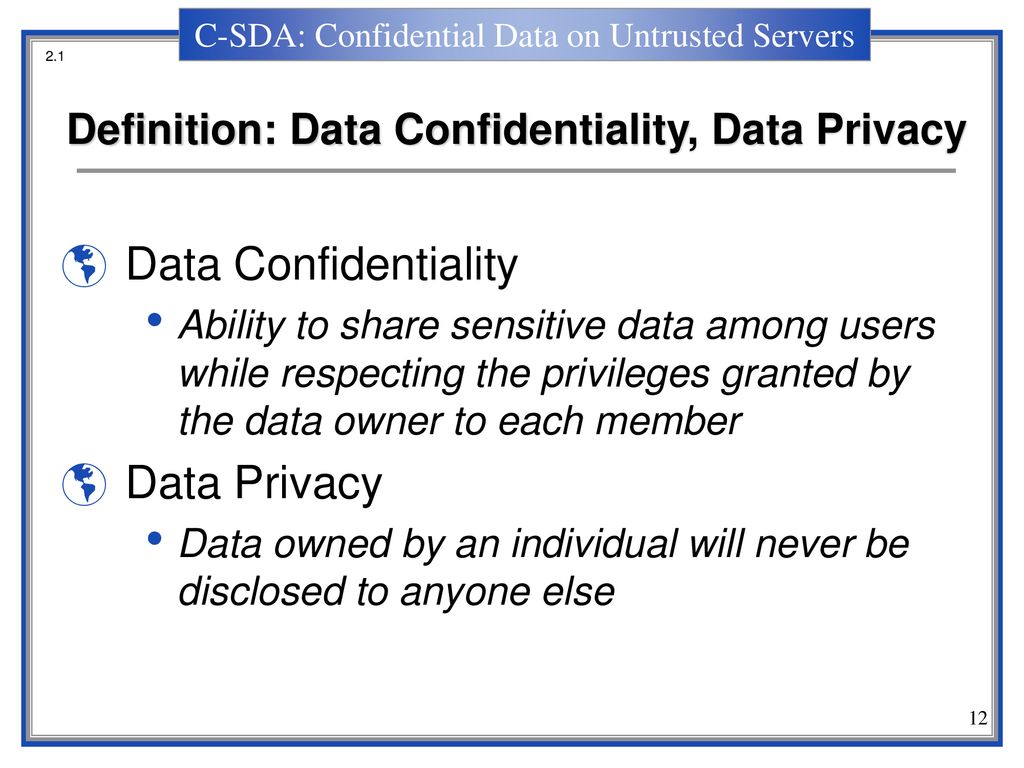
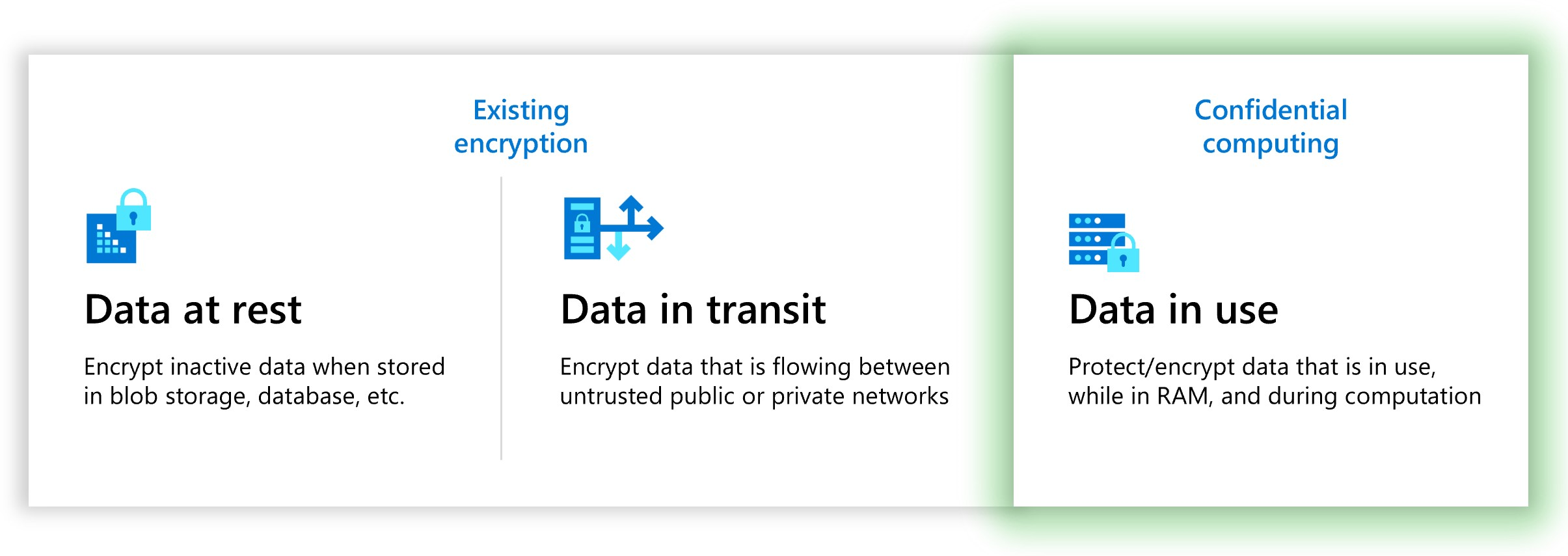
Understanding the Data Lifecycle and Five Ways to Ensure Data Confidentiality | Spiceworks It Security

Understanding the Data Lifecycle and Five Ways to Ensure Data Confidentiality | Spiceworks It Security
Privacy Preserving Machine Learning: Maintaining confidentiality and preserving trust - Microsoft Research
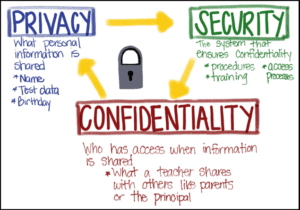
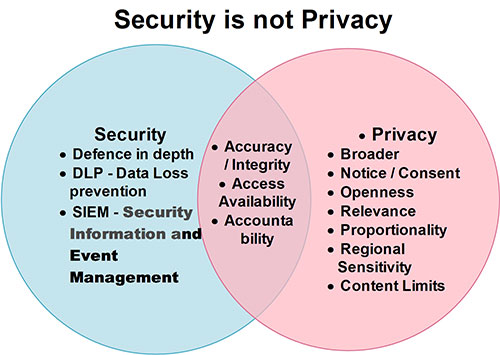
The Educator's Role: Privacy, Confidentiality, and Security in the Classroom - Student Privacy Compass


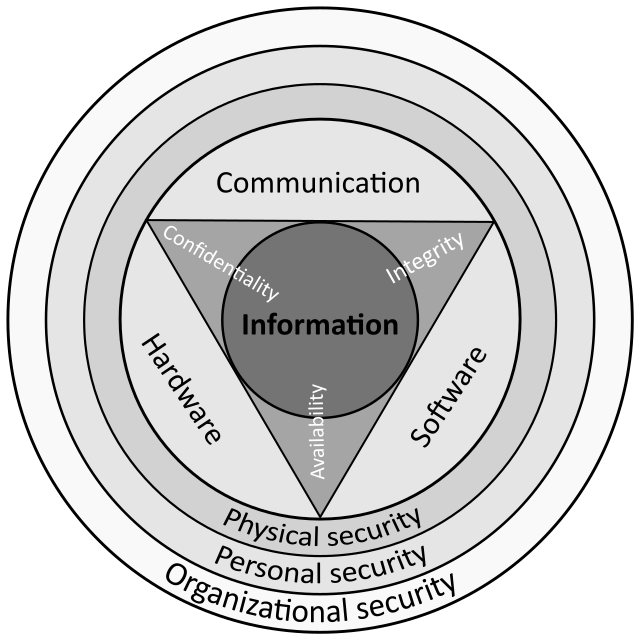



![Data Privacy vs. Data Security [definitions and comparisons] – Data Privacy Manager Data Privacy vs. Data Security [definitions and comparisons] – Data Privacy Manager](https://dataprivacymanager.net/wp-content/uploads/2019/10/Three-pillars-of-information-security-and-cybersecurity.png)




![Data Privacy vs. Data Security [definitions and comparisons] – Data Privacy Manager Data Privacy vs. Data Security [definitions and comparisons] – Data Privacy Manager](https://dataprivacymanager.net/wp-content/uploads/2019/10/Data-Privacy-vs.-Data-Security.png)